NSE8-812 Free PDF - NSE 8 - Network Security Expert 8 Written Updated: 2024

 |
 |
 |
 |
 |
 |
 |
 |
NSE8-812 NSE 8 - Network Security Expert 8 Written
Exam Specification:
- Exam Name: NSE 8 - Network Security Expert 8 Written
- Exam Code: NSE8-812
- Exam Duration: 120 minutes
- Exam Format: Multiple-choice questions
Course Outline:
1. Advanced Threat Protection
- Understanding advanced threats and attack vectors
- Implementing threat prevention and detection strategies
- Configuring advanced threat protection solutions
2. Secure Access
- Implementing secure remote access solutions
- Configuring secure access policies and authentication mechanisms
- Ensuring secure access to network resources
3. Next-Generation Firewall
- Configuring and managing next-generation firewalls
- Implementing firewall policies and rules
- Monitoring and troubleshooting firewall issues
4. Secure Email Gateway
- Deploying and managing secure email gateway solutions
- Configuring email security policies and filters
- Preventing email-based threats and spam
5. Secure Web Gateway
- Implementing secure web gateway solutions
- Configuring web filtering and content security policies
- Monitoring and blocking malicious web traffic
6. Network Security Operations and Administration
- Managing security incidents and response
- Monitoring and analyzing network traffic
- Configuring and maintaining security devices
Exam Objectives:
1. Demonstrate a deep understanding of advanced threat protection technologies and strategies.
2. Implement and configure secure access solutions for remote and local network resources.
3. Configure and manage next-generation firewalls to protect the network perimeter.
4. Deploy and manage secure email gateway solutions to prevent email-based threats.
5. Implement secure web gateway solutions for web filtering and content security.
6. Perform network security operations and administration tasks, including incident response and device configuration.
Exam Syllabus:
The exam syllabus covers the following topics (but is not limited to):
- Advanced Threat Protection
- Secure Access
- Next-Generation Firewall
- Secure Email Gateway
- Secure Web Gateway
- Network Security Operations and Administration
Fortinet Security Free PDF
Other Fortinet exams
FCESP Fortinet Certified Email Security ProfessionalFCNSA Fortinet Certified Network Security Administrator
FCNSP Fortinet Certified Network Security Professional
NSE6 Fortinet Network Security Expert 6
FortiSandbox FortiSandbox Specialist
FML-5.3.8 FML-5.3.8 FortiMail 5.3.8 Specialist
NSE8_811 Fortinet NSE 8 Written Exam
NSE4_FGT-7.0 Fortinet NSE 40 - FortiOS 7.0
NSE5_FMG-7.0 Fortinet NSE 5 - FortiManager 7.0
NSE5_FAZ-7.0 Fortinet NSE 5 - FortiAnalyzer 7.0
NSE7_EFW-7.0 Fortinet NSE 7 - Enterprise Firewall 7.0
NSE4_FGT-7.2 Fortinet NSE 4 - FortiOS 7.2
NSE8-812 NSE 8 - Network Security Expert 8 Written
NSE7_LED-7.0 NSE 7 - LAN Edge 7.0
NSE5_FSM-6.3 NSE 5 - FortiSIEM 6.3
NSE7_ADA-6.3 NSE 7 - Advanced Analytics 6.3
NSE5_EDR-5.0 Fortinet NSE 5 - FortiEDR 5.0
NSE5_FAZ-7.2 NSE 5 - FortiAnalyzer 7.2
NSE6_FAC-6.4 NSE 6 - FortiAuthenticator 6.4
NSE7_OTS-7.2 Trustworthy for Fortinet Certified Solution Specialist (FCSS)
NSE5_FCT-7.0 NSE 5 - FortiClient EMS 7.0
NSE7_SDW-7.0 Fortinet NSE 7 - SD-WAN 7.0
NSE7_PBC-7.2 Fortinet FCSS in Public Cloud Security Certification
NSE6_FNC-8.5 Fortinet NSE 6 Network Security Specialist
NSE8-812
Fortinet NSE 8 Written Exam
https://killexams.com/pass4sure/exam-detail/NSE8-812
Question #48 Section 1
Consider the following configuration setting:
Which two statements about local authentication are true? (Choose two.)
A. The FortiGate will allow the TCP connection when a ClientHello message indicating a renegotiation is received.
B. The user's IP address will be blocked 15 seconds after five login failures.
C. The user will be blocked 15 seconds after five login failures.
D. The user will need to re-authenticate after five minutes.
Answer: BD
Question #49 Section 1
You are asked to implement a single FortiGate 5000 chassis using Session-aware Load Balance Cluster (SLBC) with Active-Passive FortiControllers. Both
FortiControllers have the configuration shown below, with the rest of the configuration set to the default values.
Both FortiControllers show Master status.
What is the problem in this scenario?
A. The b1 interface of the two FortiControllers do not see each other.
B. The management interface of both FortiControllers was connected on the same network.
C. The chassis ID settings on FortiController on slot 2 should be set to 2.
D. The priority should be set higher for FortiController on slot-1.
Answer: A
Question #50 Section 1
You must create a High Availability deployment with two FortiWebs in Amazon Web Services (AWS); each on different Availability Zones (AZ) from the same region. At the same time, each FortiWeb should be
able to deliver content from the Web servers of both of the AZs.
Which deployment would fulfill this requirement?
A. Configure the FortiWebs in Active-Active HA mode and use AWS Elastic Load Balancer (ELB) for the internal Web servers.
B. Use AWS Elastic Load Balancer (ELB) for both the FortiWebs in standalone mode and the internal Web servers in an ELB sandwich.
C. Configure the FortiWebs in Active-Active HA mode and use AWS Route 53 to load balance the internal Web servers.
D. Use AWS Route 53 to load balance the FortiWebs in standalone mode and use AWS Virtual Private Cloud (VPC) Peering to load balance the internal Web servers.
Answer: B
Question #51 Section 1
Refer to the exhibit.
An administrator wants to implement a multi-chassis link aggregation (MCLAG) solution using two FortiSwitch 448D devices and one FortiGate 3700D. As described in the network topology shown in the exhibit,
two links are already connected from the FortiGate to each FortiSwitch.
What is required to implement this solution? (Choose two.)
A. Replace the FortiGate as this one does not have an ISF.
B. Create two separate link aggregated (LAG) interfaces on the FortiGate side for each FortiSwitch.
C. Add set fortilink-split-interface disable on the FortiLink interface.
D. An ICL link between both FortiSwitch devices needs to be added.
Answer: CD
Question #52 Section 1
Refer to the exhibit.
Only users authenticated in FortiGate-B can reach the server. A customer wants to deploy a single sign-on solution for IPsec VPN users. Once a user is connected and authenticated to the VPN in FortiGate-A, the
user does not need to authenticate again in FortiGate-B to reach the server.
Referring to the exhibit, which two actions satisfy this requirement? (Choose two.)
A. Use Kerberos authentication.
B. Use the Collector Agent.
C. Use FortiAuthenticator.
D. FortiGate-A must generate a RADIUS accounting packet.
Answer: CD
Question #53 Section 1
A FortiGate is used as a VPN hub for a number of remote spoke VPN units (Group A) spokes using a phase 1 main mode dial-up tunnel and pre-shared keys. You are asked to establish VPN connectivity for a
newly acquired organization's sites for which new devices will be provisioned Group B spokes.
Both existing Group A and new Group B spoke units are dynamically addressed through a single public IP Address on the hub. You are asked to ensure that spokes from Group B have different access permissions
than the existing VPN spokes units Group A.
Which two solutions meet the requirements for the new spoke group? (Choose two.)
A. Implement a new phase 1 dial-up main mode tunnel with a different pre-shared key than the Group A spokes.
B. Implement a new phase 1 dial-up main mode tunnel with certificate authentication.
C. Implement a new phase 1 dial-up main mode tunnel with pre-shared keys and XAuth.
D. Implement separate phase 1 dial-up aggressive mode tunnels with a distinct peer ID.
Answer: CD
Question #54 Section 1
You configured a firewall policy with only a Web filter profile for accessing the Internet. Access to websites belonging to the "Information Technology" category are blocked and to the "Business" category are
allowed. SSL deep inspection is not enabled on this policy.
A user wants to access the website https://www.it-acme.com which presents a certificate with CN=www.acme.com. The it-acme.com domain is categorized as
"Information Technology" and the acme.com domain is categorized as "Business".
Which statement regarding this scenario is correct?
A. The FortiGate is able to read the URL within HTTPS sessions when using SSL certificate inspection so the website will be blocked by the "Information Technology".
B. The website will be blocked by category "Information Technology" as the SNI takes precedence over the certificate name.
C. The website will be allowed by category "Business" as the certificate name takes precedence over the URL.
D. Only with SSL deep inspection enabled will the FortiGate be able to categorized this website.
Answer: B
Question #55 Section 1
Refer to the exhibit.
Central NAT was configured on a FortiGate firewall. A sniffer shows ICMP packets out to a host on the Internet egresses with the port1 IP address instead of the virtual IP (VIP) that was configured
Referring to the exhibit, which configuration change will ensure that ICMP traffic is also translated?
A.
B.
C.
D.
Answer: B
Question #56 Section 1
A company has just rolled out new remote sites and now you need to deploy a single firewall policy to all of these sites to allow Internet access using
FortiManager. For this particular firewall policy, the source address object is called LAN, but its value will change according to the site the policy is being installed.
Which statement about creating the object LAN is correct?
A. Create a new object called LAN and enable per-device mapping.
B. Create a new object called LAN and promote it to the global database.
C. Create a new object called LAN and use it as a variable on a TCL script.
D. Create a new object called LAN and set meta-fields per remote site.
Answer: A
Question #57 Section 1
Refer to the exhibit.
You are working on FortiGate 61E operating in flow-based inspection mode with various settings optimized for performance. The main Internet firewall policy is using the "default" antivirus profile. You found that
some executable virus samples files downloaded over HTTP are not being blocked by the FortiGate.
Referring to the exhibit, how can this be fixed?
A. Change the set scan-mode configuration to full.
B. Disable the emulator feature.
C. Change the set default-db configuration to extreme.
D. Add set content-disarm enable to the configuration.
Answer: A
Question #58 Section 1
Refer to the exhibit.
An organization has a FortiGate cluster that is connected to two independent ISPs. You must configure the FortiGate failover for a single ISP failure to occur without disruption.
Referring to the exhibit, which two FortiGate BGP features are enabled to accomplish this task? (Choose two.)
A. EBGP multipath
B. Graceful restart
C. Synchronization
D. BFD
Answer: BD
Question #59 Section 1
A legacy router has been replaced by a FortiGate device. The FortiGate has inherited the management IP address of the router and now the network administrator needs to remove the router from the FortiSIEM
configuration.
Which two statements about this operation are true? (Choose two.)
A. FortiSIEM will move the router device into the Decommission folder.
B. The router will be completely deleted from the FortiSIEM database.
C. By default, FortiSIEM can only parser event logs for FortiGate devices.
D. FortiSIEM will discover a new device for the FortiGate with the same IP.
Answer: AD
Question #60 Section 1
You have configured an HA cluster with two FortiGate devices. You want to make sure that you are able to manage the individual cluster members directly using port3.
Referring to the configuration shown, in which two ways can you accomplish this task? (Choose two.)
A. Create a management VDOM and disable the HA synchronization for this VDOM, assign port3 to this VDOM, then configure specific IPs for port3 on both cluster members.
B. Configure port3 to be a dedicated HA management interface; then configure specific IPs for port3 on both cluster members.
C. Allow administrative access in the HA heartbeat interfaces.
D. Disable the sync feature on port3; then configure specific IPs for port3 on both cluster members.
Answer: AB
For More exams visit https://killexams.com/vendors-exam-list

da-kuk
A good way to minimize errors in investment is to align it with macrotrends. Cybersecurity is one such trend as it deals with protecting the vast amount of data generated globally on a daily basis. Fortinet (NASDAQ:FTNT) is a good way to gain exposure to this sector as it combines several aspects I appreciate in a high-quality business: a founder at the helm who is aligned, competitive advantages, strong margins and returns, and low debt. Despite the technical challenges in the sector, I believe we can approach the investment in Fortinet from a less technical and more qualitative perspective.
Business Model
Fortinet, Inc. is one of the leading companies in the cybersecurity sector. It is a technically challenging industry with constant disruption and change. The company provides multiple solutions in the form of software and hardware for its clients. In Q3, the management announced its sales segmentation into Secure Networking, Secure Operations, and Universal SASE. They indicated their intention to expedite the transition of the business to the latter two, as they are cloud-based components. To achieve this, Fortinet has invested significantly in Point of Presence (POPs) infrastructure. A POP is a physical location in a network where devices, users, or services can connect to access other points in the network. According to Barclays Global Technology, Media & Telecommunications Conference, over the past two years, Fortinet has built 30 POPs (with another 35 in progress). Through a partnership with Google, they now have access to 180 new POPs, enabling them to catch up with competitors who typically have between 100 and 200. POPs often refer to facilities that include data centers. Nevertheless, Fortinet's strategy of building their own POPs is beneficial for future cost savings and greater vertical integration, despite the higher current capital expenditure. Additionally, Fortinet manufactures its own ASICs (application-specific integrated circuits), chips created exclusively for Fortinet's hardware and software. This in-house production enhances performance and, in the long run, reduces costs.
Market
Fortinet's Total Addressable Market is enormous, standing at $125 billion. The company's billings in 2023 are projected to reach around $5.3 billion, indicating that Fortinet currently holds only a 4% market share. This is within a highly fragmented market that is experiencing annual growth rates of 10%.
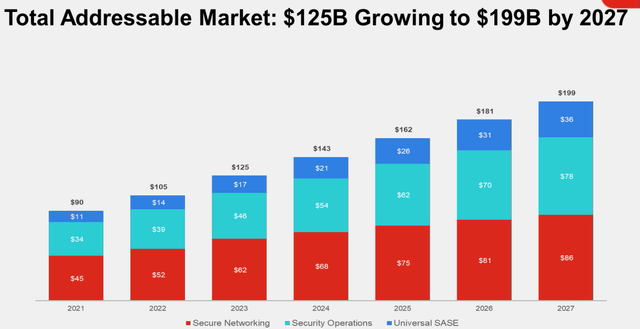
Source: Q3, 2023 Presentation
Fortinet combines a business model that sells both software and hardware. Although the hardware segment experiences slower growth and lower margins, it contributes to building an ecosystem. Once a device is installed at a customer's site, cross-selling becomes much easier. They anticipate double-digit growth for the hardware segment in the coming years. Fortinet attributes this expected growth to their superior product in this area, positioning them to gain market share when it's time for competitors' hardware replacements, as they are the largest player in this domain. However, it is highly likely that the services segment will grow at a faster rate, and since it has higher margins, we can anticipate future operational leverage for the company. Within the subscription services, there is the AI product, along with customer support, training, and repairs services.
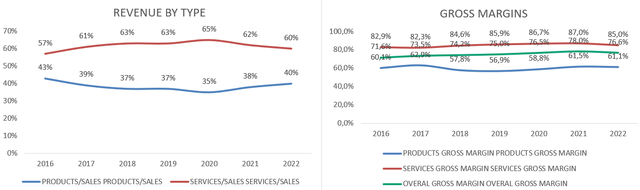
Source: Author's representation
The slowdown experienced in the Secure Networking segment (which constitutes 70% of sales), especially in the Hardware division, follows an absolute boom post-COVID, during which customers made substantial purchases. Currently, customers are more cautious about their buying decisions, leading to inventory accumulation. However, there is an expectation that inventories will return to normal levels, allowing for the satisfaction of future demand. Given the technological nature of this product, the extent of obsolescence during inventory holding is uncertain. It's worth noting that this segment has still achieved a solid 9% growth, though it previously grew at a rapid pace of 40%. Despite facing a challenging comparison base, the company has managed to maintain a commendable growth rate.
Moreover, it's essential to consider that these cycles typically last two years, implying that we might be at the midpoint of the cycle, and the market could soon start factoring in its conclusion. As illustrated, sales are a lagging indicator, and attention should be directed towards Billings for a more timely assessment.
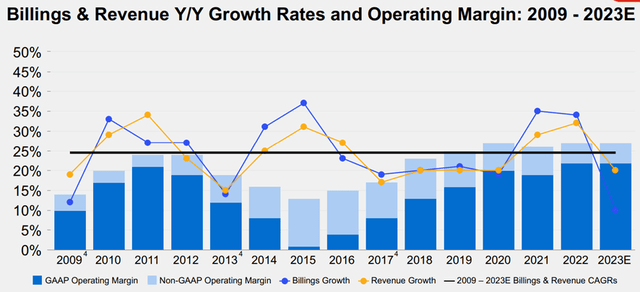
Source: Q3'23 Investor Slides
Management and Capital Allocation
If management by itself is one of the most important aspects of a company, in a sector as disruptive as cybersecurity, investing in a management team we can trust is extremely important. The founders, Ken Xie and Michael Xie, have been with the company since the year 2000, and together they control more than 15% of the outstanding shares. Their interests are fully aligned with the shareholders. Their extensive knowledge of the sector is significant, and their capital allocation strategy has been very effective.
The Net Income to Free Cash Flow conversion is over 100%, thanks to it being a subscription-based business. Most of the free cash flow has been allocated to share buybacks (reducing outstanding shares by -10% over the last 7 years) and some small acquisitions. Stock options represent 5% of sales and 14% of Operating Cash Flow, with a decreasing trend. This is quite favorable for a technology company. The company operates without debt and S&P Global rates Fortinet's credit category as BBB+. 90% of the capital allocated to "innovation" has been invested in research and development, with the remaining portion dedicated to merger and acquisition activities.
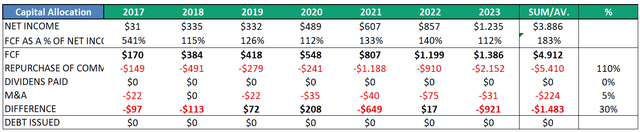
Source: Author's representation
Competitive Advantages
In my opinion, the key strength of this company lies in its unified platform, FortiOS (Fortinet Investor Relations Presentation, slide 31), which integrates various products and services rather than creating standalone solutions that are difficult to integrate. This not only generates a network effect but also presents high switching costs for customers, potentially leading to pricing power. The ecosystem created by the company makes it indispensable for the customer.
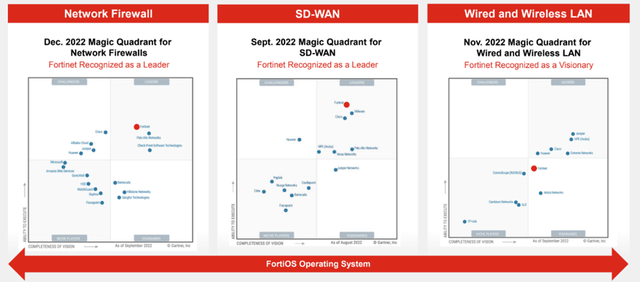
Source: Investor Relations Presentation
Financials
Fortinet's financials are impeccable. It has experienced very high double-digit growth in all its figures. For example, sales have grown at a rate of 23.5% (6-year CAGR), while FCF/share has grown at a rate of 63.5% (6-year CAGR), driven by operational leverage and share buybacks. This operational leverage has been due to a significant expansion of margins; for instance, the EBIT margin has increased from 7% in 2017 to an estimated 27% for the fiscal year 2023, although I will provide further commentary on this below. The returns are impressive, with average ROICs exceeding 100% in recent years. They also maintain a net cash position, with only around $1 billion in debt. Lastly, they follow an asset-light business model, where maintenance CAPEX ranges from 2% to 3% of sales.
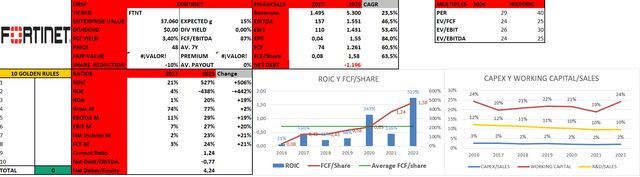
Source: Author's representation
In the Barclays Conference, management also discussed something about the margins. In the long term, their target is 25%, but the senior vice president mentioned that he wanted the flexibility to invest in marketing, R&D, or whatever was necessary to grow the business without being constrained by the margin. In their models, a 25% margin is feasible, especially as the services segment is expected to grow more than hardware. The 27% margin from last year was attributed to the strength of the dollar, as they invoiced in dollars but paid 70% of their staff in their local currencies (which were depreciated at that time). I always appreciate a management team focused on the long-term sustainability of the business, even if it means impacting current accounting with investments that enhance their competitive advantages.
Valuation
To evaluate Fortinet, I will use a discounted cash flow model, incorporating a discount rate of 10%, a terminal growth rate of 3%, and a free cash flow growth of 15% (historically, it has been 60% CAGR in recent years). With these assumptions, the calculated fair value for Fortinet is $60 per share. If we consider a scenario with higher growth, such as 20%, the fair value would be $85 per share. However, to account for this increased growth, it might be more appropriate to raise the discount rate to 12%, in which case the fair value would be $63. In any case, I believe that Fortinet's stock is undervalued, and that's why I rate the stock as a buy.
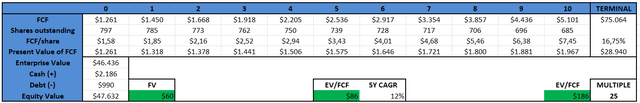
Source: Author's representation
Risks
It is worth noting that 57% of total sales come from only three distributors. In the FY21 annual report, it's mentioned that the Exclusive distributor accounted for 31% of sales. This significant concentration not only poses a risk in itself but also raises the consideration that these distributors might resell products from competitors and could be incentivized to favor these competitors in the future, potentially at the expense of Fortinet. Nevertheless, the risk of these distributors severing ties with Fortinet, one of the top companies in the sector, seems remote. It's akin to a sports channel specializing in football, breaking agreements with the Premier League and ceasing to broadcast it. Clearly, it's a lose-lose situation for both parties. Furthermore, another major client would likely seek to absorb this new volume and gain an advantage over others. The situation appears unlikely, despite the increasing customer concentration, as these dynamics are inherent to the sector. For example, Palo Alto Networks also has 50% of its sales with three clients (cybersecurity application providers).
Inventory Risks: The accumulation of hardware devices in inventories may not always be favorable. While it enables the company to meet growing demand when the cycle changes, there is a risk of obsolescence in a rapidly evolving sector. Furthermore, 88% of their hardware is produced in Taiwan, which could be impacted in the event of a future conflict with China. However, the company likely has contingency plans in place to address this potential issue if it arises.
Disruption Risk: Given the rapid emergence and evolution of new threats today, Fortinet has a dedicated department responsible for identifying these emerging threats. They investigate these threats using AI and subsequently develop corresponding mitigations to distribute to subscribed customers. It's noteworthy that customers pay for subscriptions to benefit from these services for a period ranging from 1 to 5 years. Furthermore, thanks to its scale, Fortinet has a very high R&D budget in absolute terms, as well as an extensive customer distribution. All of this is complemented by founders at the helm with deep knowledge of the industry.
Conclusion
In conclusion, I believe Fortinet is a great company for having exposure to the cybersecurity sector. The lack of expertise can be mitigated by placing trust in a well-aligned management team with expertise in the field. Additionally, the fantastic fundamentals and scale provide protection against disruptive threats. The company can also defend itself through the ecosystem it creates by combining software and hardware, even as it increasingly focuses on the more profitable segments of services. Overall, I find the price attractive, and I anticipate satisfactory long-term results.
Copyright © 2024 CyberRisk Alliance, LLC All Rights Reserved. This material may not be published, broadcast, rewritten or redistributed in any form without prior authorization.
Your use of this website constitutes acceptance of CyberRisk Alliance Privacy Policy and Terms & Conditions.
SUNNYVALE, Calif., Dec. 18, 2023 (GLOBE NEWSWIRE) -- Fortinet® (NASDAQ: FTNT), the global cybersecurity leader driving the convergence of networking and security, today announced the latest release of new, integrated operational technology (OT) security solutions and services. These additions further distance Fortinet’s industry-leading OT Security Platform from the rest of the market.
“We understand that OT differs significantly from traditional IT systems, and that’s why our OT Security Platform was purpose-built to provide integrated protection and risk management specific to industrial environments,” said John Maddison, Chief Marketing Officer and EVP, Product Strategy at Fortinet. “Rising attacks on critical infrastructure have made OT security more important than ever before. With today’s news, Fortinet continues to empower customers with the most sophisticated OT solutions and intelligence in the industry.”
The Need for Integrated OT-Specific Security
The number of industrial devices connected beyond their network boundaries is rapidly increasing, and CISOs now face skyrocketing risks across their OT environments. In fact, Fortinet found that three-fourths of OT organizations reported at least one intrusion in the last year, and nearly one-third reported being victims of a ransomware attack. To solve this challenge, organizations need an integrated security approach designed specifically for industrial solutions that enables policy enforcement across the entire attack surface, consolidates point products, and reduces operational overhead.
Bolstering the Fortinet OT Security Platform with New and Enhanced Offerings
The Fortinet OT Security Platform is an integrated portfolio of cybersecurity products, solutions, and security services designed specifically for industrial networks and powered by real-time OT threat intelligence. Because the OT Security Platform is a part of the Fortinet Security Fabric, it empowers customers with deep visibility across their entire environment and securely facilitates IT/OT convergence. The platform also gives organizations the ability to implement a zero-trust model within OT environments, including secure remote access to OT assets and systems for remote employees and contractors.
OT Security Platform updates announced today, which build on improvements unveiled earlier this year, span two key pillars of the Security Fabric:
Secure Networking for OT
- The new FortiSwitch Rugged 424F is an industrial-class ethernet switch (IES) designed to address the requirements of digital substations and the power utility industry. The switch supports real-time OT networking protocols and integrates with FortiGate Next-Generation Firewalls (NGFWs) for comprehensive security and access control.
- The new FortiAP 432F access point meets Class 1, Division 2 requirements for use in hazardous OT environments. It can segment industrial Wi-Fi networks to prevent attacks from spreading across unprotected devices and systems. This expansion of the IP67-rated access-point line now enables the deployment of additional OT applications in industries such as oil and gas.
- The new FortiExtender Vehicle 211F wireless gateway is a semi-ruggedized mobility solution for connected fleets, mobile systems, and OT deployments. It was also designed to meet the requirements of the AT&T FirstNet wireless communications network for first responders.
- FortiOS, Fortinet’s operating system, has been updated with the OT View dashboard, which correlates and displays important OT data. This dashboard makes it easy for organizations to understand their entire attack surface—both IT and OT—and take action from a single console.
Security Operations and Services for OT
- FortiAnalyzer now includes OT-specific analytics, risk, and compliance reports, providing security operations teams with faster threat detection, asset and vulnerability correlation, and reporting.
- FortiNDR, which supports on-premises, cloud, and hybrid deployments, can now analyze more than 15 different OT-network protocols. It also includes AI-powered OT-network behavior analysis to identify malicious network activity and files.
- FortiDeceptor, Fortinet’s deception technology for early breach and attack isolation, now supports 30 OT protocols and additional OT decoys to protect diverse industrial environments.
- The FortiGuard OT Security Service boasts the industry’s deepest OT threat intelligence database and now covers more than 70 OT protocols and more than 4,000 OT application and device vulnerability signatures. These signatures enable strict access control policies on network traffic and provide virtual patching for vulnerable OT assets.
- FortiGuard Outbreak Alerts, an industry-leading cybersecurity resource, now includes critical information about OT-specific threats. This empowers customers with the information they need to harden their systems against new and emerging attacks following the NIST Cyber Security Framework.
"IT and OT are converging and these colliding environments are increasing overall risk. Our clients require robust OT solutions and services without extensive deployments that complicate administration and place additional strain on IT and security teams. Through the Fortinet OT Security Platform, we can provide clients with a unified approach of safeguarding both the carpeted side of a business as well as the concrete side of the business. We eagerly anticipate introducing these updated and novel offerings to our customer community." – Dan Sanderson, VP of Strategy, Cyber Advisors
Additional Resources
- Learn more about the Fortinet OT Security Platform and the enhancements announced today.
- Watch the video to learn more about how Fortinet delivers cybersecurity for industrial controls and OT environments.
- Read about how Fortinet OT customers are securing their organizations.
- Learn more about the Fortinet Open Ecosystem and Fabric-Ready Technology Alliance Partner Program.
- Learn more about Fortinet’s free cybersecurity training, which includes broad cyber awareness and product training. As part of the Fortinet Training Advancement Agenda (TAA), the Fortinet Training Institute also provides training and certification through the Network Security Expert (NSE) Certification, Academic Partner, and Education Outreach programs.
- Follow Fortinet on Twitter, LinkedIn, Facebook, and Instagram. Subscribe to Fortinet on our blog or YouTube.
About Fortinet
Fortinet (NASDAQ: FTNT) is a driving force in the evolution of cybersecurity and the convergence of networking and security. Our mission is to secure people, devices, and data everywhere, and today we deliver cybersecurity everywhere you need it with the largest integrated portfolio of over 50 enterprise-grade products. Well over half a million customers trust Fortinet's solutions, which are among the most deployed, most patented, and most validated in the industry. The Fortinet Training Institute, one of the largest and broadest training programs in the industry, is dedicated to making cybersecurity training and new career opportunities available to everyone. FortiGuard Labs, Fortinet’s elite threat intelligence and research organization, develops and utilizes leading-edge machine learning and AI technologies to provide customers with timely and consistently top-rated protection and actionable threat intelligence. Learn more at https://www.fortinet.com, the Fortinet Blog, and FortiGuard Labs.
FTNT-O
Copyright © 2023 Fortinet, Inc. All rights reserved. The symbols ® and ™ denote respectively federally registered trademarks and common law trademarks of Fortinet, Inc., its subsidiaries and affiliates. Fortinet’s trademarks include, but are not limited to, the following: Fortinet, the Fortinet logo, FortiGate, FortiOS, FortiGuard, FortiCare, FortiAnalyzer, FortiManager, FortiASIC, FortiClient, FortiCloud, FortiMail, FortiSandbox, FortiADC, FortiAI, FortiAIOps, FortiAntenna, FortiAP, FortiAPCam, FortiAuthenticator, FortiCache, FortiCall, FortiCam, FortiCamera, FortiCarrier, FortiCASB, FortiCentral, FortiConnect, FortiController, FortiConverter, FortiCWP, FortiDB, FortiDDoS, FortiDeceptor, FortiDeploy, FortiDevSec, FortiEdge, FortiEDR, FortiExplorer, FortiExtender, FortiFirewall, FortiFone, FortiGSLB, FortiHypervisor, FortiInsight, FortiIsolator, FortiLAN, FortiLink, FortiMoM, FortiMonitor, FortiNAC, FortiNDR, FortiPenTest, FortiPhish, FortiPlanner, FortiPolicy, FortiPortal, FortiPresence, FortiProxy, FortiRecon, FortiRecorder, FortiSASE, FortiSDNConnector, FortiSIEM, FortiSMS, FortiSOAR, FortiSwitch, FortiTester, FortiToken, FortiTrust, FortiVoice, FortiWAN, FortiWeb, FortiWiFi, FortiWLC, FortiWLM and FortiXDR. Other trademarks belong to their respective owners. Fortinet has not independently verified statements or certifications herein attributed to third parties and Fortinet does not independently endorse such statements. Notwithstanding anything to the contrary herein, nothing herein constitutes a warranty, guarantee, contract, binding specification or other binding commitment by Fortinet or any indication of intent related to a binding commitment, and performance and other specification information herein may be unique to certain environments.
| Media Contact: | Investor Contact: | Analyst Contact: |
| Margaret Reeb Fortinet, Inc. 408-235-7700 pr@fortinet.com |
Peter Salkowski Fortinet, Inc. 408-331-4595 psalkowski@fortinet.com |
Brian Greenberg Fortinet, Inc. 408-235-7700 analystrelations@fortinet.com |


Cybersecurity firm Fortinet Inc. today announced a new generative artificial intelligence assistant that accelerates threat investigation and remediation.
Called Fortinet Advisor, the new AI service is designed to augment the capabilities of security operations teams. Integrated with Fortinet’s security information and event management service, called FortiSIEM, and security orchestration, automation and response solution, called FortiSOAR, the AI analyzes security incidents and provides easy-to-understand summaries, context and potential impact assessments.
Fortinet Advisor assists in building complex investigation queries and creating efficient remediation plans. In doing so, it significantly reduces the time required for threat detection and response, enhancing the overall efficiency and effectiveness of SecOps teams in managing cybersecurity threats and incidents.
The tool’s integration with FortiSIEM and FortiSOAR is part of Fortinet’s commitment to providing comprehensive cybersecurity solutions. Working within the established framework of these platforms, Fortinet Advisor ensures a seamless workflow for security professionals, allowing them to focus on strategic decision-making rather than getting bogged down by the intricacies of data analysis.
Part of Fortinet’s Security Operations portfolio, the service can help organizations move from a reactive to a proactive security posture and quickly detect and disrupt cyber threats. Fortinet’s Security Operations solutions utilize AI and advanced analytics to identify sophisticated threats early in the kill chain and automate response activity across the Fortinet Security Fabric to speed investigation and remediation.
The new AI is not Fortinet’s first entry into AI, with the company now having a portfolio of more than 40 AI-powered offerings. “We’re excited to build on our legacy as a leader in AI cybersecurity innovation with Fortinet Advisor, which combines Fortinet’s vast intelligence network with the benefits of GenAI to increase security team productivity and speed threat detection and mitigation,” Michael Xie, founder, president and chief technology officer at Fortinet, said ahead of the release.
Fortinet was previously in the news last month when it announced a company restructuring to sharpen its focus on core growth areas after its revenue and outlook fell short in its fiscal third quarter. The plans include leveraging scale, go-to-market capabilities and engineering expertise to focus attention on the fast-growing SASE and security operations markets.
Image: Fortinet
Your vote of support is important to us and it helps us keep the content FREE.
One click below supports our mission to provide free, deep, and relevant content.
Join our community on YouTube
Join the community that includes more than 15,000 #CubeAlumni experts, including Amazon.com CEO Andy Jassy, Dell Technologies founder and CEO Michael Dell, Intel CEO Pat Gelsinger, and many more luminaries and experts.
THANK YOU
NSE8-812 Questions and Answers | NSE8-812 course outline | NSE8-812 student | NSE8-812 basics | NSE8-812 learning | NSE8-812 health | NSE8-812 Free PDF | NSE8-812 benefits | NSE8-812 Topics | NSE8-812 download |
Killexams Exam Simulator
Killexams Questions and Answers
Killexams Exams List
Search Exams